Distributed multichannel medium access control protocol without common control channel for single-hop cognitive radio networks
来源期刊:中南大学学报(英文版)2011年第5期
论文作者:徐贵森 谭学治
文章页码:1532 - 1544
Key words:cognitive radio network; multichannel cognitive radio; MAC (medium access control) protocols; performance evaluation; saturation throughput
Abstract:
A novel distributed cognitive radio multichannel medium access protocol without common control channel was proposed. The protocol divided a transmission interval into two parts for exchanging control information and data, respectively. In addition to evaluating system saturation throughput of the proposed protocol, a three-dimensional multi channel Markov chain model to describe the sate of the cognitive users (CUs) in dynamic spectrum access was presented. The proposed analysis was applied to the packet transmission schemes employed by the basic, RTS/CTS access mechanism adopted in the normal IEEE 802.11. Analyzing the advantage of the two methods, a hybrid access mechanism was proposed to improve the system throughput. The simulation results show that the experiment results are close to the value computed by the model (less than 5%), and the proposed protocol significantly improves the performance of the system throughput by borrowing the licensed spectrum. By analyzing the dependence of throughput on system parameters, hybrid mechanism dynamically selecting access mechanism can maintain high throughput.
J. Cent. South Univ. Technol. (2011) 18: 1532-1544
DOI: 10.1007/s11771-011-0870-8![]()
XU Gui-sen(徐贵森), TAN Xue-zhi(谭学治)
Department of Communication Research Center, Harbin Institute of Technology, Harbin 150080, China
? Central South University Press and Springer-Verlag Berlin Heidelberg 2011
Abstract: A novel distributed cognitive radio multichannel medium access protocol without common control channel was proposed. The protocol divided a transmission interval into two parts for exchanging control information and data, respectively. In addition to evaluating system saturation throughput of the proposed protocol, a three-dimensional multi channel Markov chain model to describe the sate of the cognitive users (CUs) in dynamic spectrum access was presented. The proposed analysis was applied to the packet transmission schemes employed by the basic, RTS/CTS access mechanism adopted in the normal IEEE 802.11. Analyzing the advantage of the two methods, a hybrid access mechanism was proposed to improve the system throughput. The simulation results show that the experiment results are close to the value computed by the model (less than 5%), and the proposed protocol significantly improves the performance of the system throughput by borrowing the licensed spectrum. By analyzing the dependence of throughput on system parameters, hybrid mechanism dynamically selecting access mechanism can maintain high throughput.
Key words: cognitive radio network; multichannel cognitive radio; MAC (medium access control) protocols; performance evaluation; saturation throughput
1 Introduction
Because of the current fixed-frequency allocation scheme, the spectrum is becoming a major bottleneck. However, researches show that lots of the spectra remain unused at a given time and location, so a more flexible allocation strategy needs to be proposed to solve the spectrum scarcity problem. This observation has recently led to the new paradigm of opportunistic spectrum access, where users can actively search for unused spectrum in licensed bands and communicate using these spectrum holes.
As cognitive radio networks (CRNs) generally need to use several channels to fully utilize the spectrum holes and avoid interfering with the primary users (PUs), a centrally controlled cognitive radio (CR) scheme has been standardized in the IEEE 802.22 Working Group, which defines the physical and MAC layers for a novel air interface based on the cognitive radio paradigm [1]. The aim is to provide a standard for wireless regional area networks by exploiting unused spectrum in the TV bands. The core components of IEEE 802.22 system are the base stations (BSs) and the consumer premise equipments (CPEs) [2]. BS and CPEs perform channel sensing periodically. If any of the channels used by IEEE 802.22 network is occupied by the licensed incumbents, the primary task of IEEE 802.22 devices would vacate the channels and switch to some other unused channels. Recently, a wide variety of algorithms managing various aspects of cognitive radio networks based on the multichannel medium access control have been proposed. Many of these algorithms that coordinate a cognitive radio network, however, require the existence of a commonly known and globally available control channel, through which the BSs can transmit or receive the information (spectrum management decisions [3], configuration instructions [4-5], routing information [6] or multichannel medium access information [7]) distributed among the network nodes. However, without such information, the performance of the cognitive radio algorithms is significantly deterred or the algorithm may not function properly at all. Thus, possessing such a common global control channel for active coordination is crucial for many applications. If such a channel is statically assigned, one has to make sure that the network nodes are always allowed to use it, i.e., one must license the spectrum or operate in a license-free band, and also is aware that such channel acts as the critical link in the network (the strategy is against the original concept of the cognitive radio dynamic spectrum access). If it becomes suddenly unavailable, the cognitive radio net-work loses its ability to coordinate and adapt.
Beside such centrally controlled solutions with common control channel, a distributed CR scheme exists, which would enable cognitive behavior in mesh or ad hoc networks [8-10]. Distributed control reduces the infrastructure cost, as well as provides larger flexibility and robustness.
Much of the theoretical foundation is proposed to describe the single-hop network with single channel for cognitive radio network [11]], where a cognitive radio communication network routing policy with single channel was proposed [12]. Subsequently, numerous studies have addressed to focus on the performance of the delay and throughput [13].
In this work, we also focus on the improvement of the throughput and then develop a multichannel cognitive radio MAC (MCRMAC) protocol without common control channel to dynamically transport control information before data in several selected channels at run-time. The protocol is able to protect the licensed users from CR interference even if these licensed users are hidden (i.e., when a communication interferes with the licensed user, but neither source nor destination is able to scan the licensed user). This is done through distributed sensing. Energy consumption also become a key concern. Today, there is a continuously growing gap between the available energy, resulted from the battery technology evolution and the exponentially increasing energy requirements of emerging radio systems and applications. This is particularly true for reconfigurable radio implementations, which are seen as enablers for CR systems [14]. Based on enabling opportunistic spectrum sharing, the proposed MCRMAC protocol is designed by taking this energy constraint into account.
The main contribution of this work is the design of a MCRMAC protocol without common control channel for CRNs. By allowing the CUs to enter a doze state when no communication takes place, the MAC protocol achieves energy-efficient communication. Furthermore, we propose an analytical model to describe the multichannel completion state of each communicating node. The model allows to calculate the saturation throughput performance of two distributed coordination function access mechanisms (basic, RTS/CTS access mechanisms) and then a hybrid access mechanism is proposed to combine the advantage of above two methods.
2 Presentation of MCRMAC protocol
In this section, we describe the considered network scenario and the radio architecture assumed for communication and sensing, and introduce the novel multichannel cognitive radio medium access control protocol that enables opportunistic spectrum sharing. By borrowing licensed spectrum, this protocol enables significant throughput increase, as well as a potential energy decrease. Since borrowing licensed spectrum has to be done with care, the protocol is designed to protect PUs from CR interference even in hidden terminal situations.
2.1 Network scenario
The cognitive radio network scenario is of interest because of the potential for the great gains in spectral efficiency and network performance [15]. In this work, we assume the following distributed hierarchical scenario. The principle specifies two technologies. One is free communication technology of the primary users, which has the rights for interference-free communication in certain channels. When unused by the PUs, these channels can be used for CUs communication. The CUs that interfere with a PU have to vacate the channel as soon as possible before the PU has started communicating on the channel. The other is distributed sensing technology. In order to accurately measure which channel is currently used by PUs, the CUs need to collaborate to get a common spectral view. In Fig.1, when CU A transmits to CU B, a PU B is interfered. However, as PU B is outside the detectability range, it has no way of knowing this. This case is a classical hidden terminal problem that can be solved by distributed sensing technology. If CU C, which is inside the transmission range, notifies CU B before the data transmission, then the communication between A and B can be stopped or moved to another channel to avoid the interference with the PUs. The specific implementation of the distributed sensing technique is done. For distributed sensing, the OR rule is assumed. Here, a channel is declared occupied if at least one terminal thinks the channel as occupied [16].
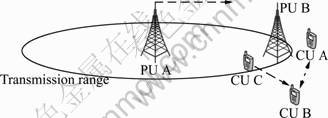
Fig.1 Distributed sensing technology for cognitive radio network
2.2 Assumptions
Before describing the protocol in detail, firstly some assumptions are summarized.
1) q channels are available for use, and all channels have the same bandwidth. None of these channels overlap, so the packets transmitting over different channels do not interfere with each other. This is (approximately) true for orthogonal techniques like orthogonal frequency-division multiplexing (OFDM).
2) All CUs have the synchronization algorithm, and the synchronization algorithm used is the timer synchronization function (TSF) of the IEEE 802.11 MAC protocol [17].
3) Each CU is equipped with a single-transmitter and single-receiver, so in a fixed time, the CU stays in only one channel to transmit or receive packets.
4) The interfaces are capable of dynamically switching their channel with the global timer.
5) The active period of the PUs is substantially longer than the length of the CR beacon interval. Within the IEEE 802.22, where a TV station stays active for more than a few hours, this is certainly true. In other cases, we can adapt the beacon interval to achieve this.
2.3 Control information window
Figure 2 shows that the global time is divided into fixed length beacon intervals, in which we can distinguish two phases: the control information window and the DATA window. During the control information window, the CUs participate in the following phases:
1) Fast scan
Due to the assumption of the synchronization algorithm, all CUs synchronize with global timer. After the start of the CIW, the CUs perform a fast scan for each channel. This scan is used to update the channel state list (CSL) value of the scanned channel, which contains the local view of CUs on the channel. It has three types of entries:
 (1)
(1)
If the value of CSL is confirmed, then no further or preparing transmission action is taken in the channel.
Otherwise, the CSL value is updated to zero, which stands for uncertainty. The fine scan will be carried on in the DW. The protocol is also capable of supporting other channel selection strategies.
2) CSL information exchange
CUs learn the network spectrum opportunities by listening and broadcasting the CSL packets. After the fast scan phase, CUs compete to broadcast their CSL packets in fixed length time per channel. Firstly, all CUs broadcast their CSL packets with the back-off algorithm (introduced in 2.4 DATA window). The CU does not transmit its CSL packet in the channel, when it senses that the result of the CSL is equal to 0 or 1. Secondly, each CU compares the received CSL packets with its own. If it is different, the CU will update the CSL with the OR rule, and then broadcast the new CSL packet. Otherwise, the CU that broadcasts none of the CSL packet needs to transmit the received packet to its neighbor CUs, and the CU that has transmitted a CSL packet takes no further action. The proposed CSL information exchange algorithm is an efficient physical OR implementation, since it avoids all MAC overheads as compared with the case where every CU has to transmit its own CSL packet to other CUs continually.
After the information exchange phase, a generally accepted CSL can be maintained by every CU. As shown in Fig.3, if a channel is detected (CSL[i]=1), then the channel needs to be closed to avoid the interference with the PU. The second case is that when uncertainty exists about the detection result (CSL[i]=0), and then the uncertain channel now needs to perform a fine scan in this channel with cooperative detection or other detection algorithms.
3) Preoccupation channel
In this phase, CUs need to preoccupy a channel for transmitting the data in the DW. Traffic is indicated with two-way handshakes. Nodes that have buffered packets indicate traffic by sending preoccupation frames on the random available channel with the back-off algorithm in the rest time of the CIW. Each node overhears the preoccupation frames in each available channel, according to the global timer. If the destination node agrees with the selected channel, then it replies with a preoccupation-ACK frame. After the CIW, the nodes that have exchanged preoccupation frames stay awake until they have completed data exchange. The nodes that neither transmitted nor received preoccupation frames enter a doze state until the next time of the CIW.
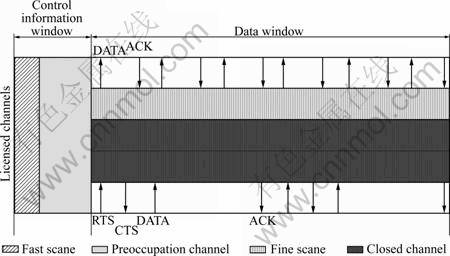
Fig.2 Division of beacon interval
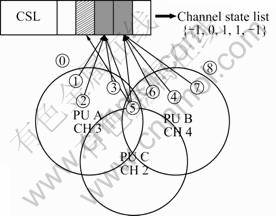
Fig.3 Common view of channel state list (CSL)
2.4 DATA window
The DATA window is used for data exchange and fine sensing. In this phase, nodes that have set the CSL to uncertain state perform a fine scan of the corresponding channel, which is free of CR traffic. This can be done by some of idle nodes in parallel with communication on another channel as it is assumed that the CUs have a dedicated sensing engine. The CSL value for this channel will be updated to the outcome of the fine scan in the next bacon interval. As shown in Fig. 2, data exchange follows the modified IEEE 802.11 distributed coordination function (DCF) multi-channel procedure with basic RTS/CTS exchange in the preoccupied channel. An additional feature is that nodes are allowed to enter a doze state when they complete data exchange in the DATA window (i.e., if the transmit queue is empty).
1) Multichannel exponential back-off algorithm
The normal DCF of IEEE 802.11 relies on a continuous sensing of the wireless channel. A node with a new packet to transmit monitors the channel activity. If the channel is idle for a period of time equal to a distributed interframe space (DIFS), the station transmits. Otherwise, if the channel is sensed to be busy (either immediately or during the DIFS), the node persists to monitor the channel until it is measured to be idle for a DIFS. At this point, the station generates a random back-off interval before transmitting (this is the collision avoidance feature of the protocol), to minimize the probability of collision with packets being transmitted by other nodes. In addition, to avoid channel capture, a node must wait a random back-off time between two consecutive new packet transmissions, even if the medium is sensed to be idle in the DIFS time [1].
In this protocol, each of the available channels obeys the principle of IEEE 802.11 DCF to transmit data, and an exponential back-off algorithm is adopted. At each packet transmission in the selected channel, the back-off time is uniformly chosen in the range of [0, W-1], where W is the contention window, and depends on the number of transmissions failed for the packet. At the first transmission attempt, W is set equal to a value Wmin called minimum contention window. After each unsuccessful transmission, W is doubled, up to a maximum value Wmax=2mWmin (m is the maximum back-off stage). And then, the node that selects the next available channel in turn competes the opportunity of transmitting data. In the new channel, W recovers the original value Wmin; however, at the last channel, W has been up to the maximum value; after another unsuccessful transmission, W is unchanged.
2) Basic access mechanism (two-way)
The basic access mechanism is a two-way handshaking technique, which is characterized by the immediate transmission of a positive acknowledgement (ACK) by the destination node, upon successful reception of a packet transmitted by the source node [18].
Since the carrier sense multiple access with collision avoidance (CSMA/CA) does not rely on the capability of the node to detect a collision by hearing its own transmission, an ACK is transmitted by the destination node to signal the successful packet reception. The ACK is immediately transmitted at the end of the packet, after a period of time called short interframe space (SIFS). As the SIFS is shorter than DIFS, no other node is able to detect the channel idle for a DIFS until the end of the ACK. If the transmitting node does not receive the ACK within a specified ACK_Timeout, or it detects the transmission of a different packet on the channel, it reschedules the packet transmission according to the given back-off rules.
Figure 4 shows that two nodes A and B compete the same wireless channel with basic access mechanism. At the beginning of node A transmitting its packet, the node B sensing the channel is busy with its back-off time counter at 3, and at the end of the ACK transmission, the channel is idle again. Both nodes A and B wait for a DIFS and then node A reselects a back-off time equal to 5. The back-off time counter is reactive to decrement in the back-off phase. The node B transmits its packet B1 when the back-off time counter reaches zero.
3) RTS/CTS access mechanism (four-way)
DCF defines an additional four-way handshaking technique to be optionally used for a packet transmission [19]. This mechanism, known as RTS/CTS, is shown in Fig. 5. A node that wants to transmit a packet, waits until the channel is sensed to be idle for a DIFS, follows the back-off rules explained above, and then, instead of the packet, preliminarily transmits a special short frame called request to send (RTS). When the destination node detects the RTS frame, it responds, after a SIFS, with a clear to send (CTS) frame. The source node is allowed to transmit its packet only if the CTS frame is correctly received. The frames RTS and CTS carry the information of the length of the packet to be transmitted. This information can be read by any listening node, which is then able to update a network allocation vector (NAV) containing the information of the period of time in which the channel will remain busy. Therefore, when a node is hidden from either the source or the destination node, by detecting just one frame among the RTS and CTS frames, it can suitably delay further transmission, and thus avoid the collision. The RTS/CTS mechanism is very effective in terms of system performance, especially when large packets are considered, as it reduces the length of the frames involved in the contention process. In fact, in the assumption of perfect channel sensing by every node, collision may occur only when two (or more) packets are transmitted within the same slot time. If both source nodes employ the RTS/CTS mechanism, collision occurs only on the RTS frames, and it is early detected by the source nodes by the lack of CTS responses.
4) Hybrid access mechanism
In the proposed protocol, a hybrid access mechanism can be adopted to increase the network performance. Packets are transmitted by means of the RTS/CTS mechanism only if ![]() (the throughput of system with RTS/CTS access mechanism is more than that with basic access mechanism), and vice verse.
(the throughput of system with RTS/CTS access mechanism is more than that with basic access mechanism), and vice verse.
3 System throughput analysis
Many MAC protocols exhibit some forms of instability with increasing the payload, especially in the cognitive radio network scenario. Figure 6 shows the unstable behavior of our proposed protocol. The considered network scenario contains ten cognitive radio nodes, which form five communication links. All the nodes can transmit packets at two available channels. In the assumption that PUs occupy a channel to communicate from 50 s to 65 s, we have run simulations, in which the ideal load linearly increases with the simulation time. The simulation parameters employed are summarized in Table 1. The straight line represents the ideal load, normalized with respect of the channel capacity. The throughput has been generated through varying the transfer rate to match the ideal load. From Fig.6, we can see that the measured throughput follows the ideal load in most of simulation time, while it extremely drops after 75 s without the PU interference. This extreme throughput value is referred to saturation throughput, and represents the system throughput in overload condition [20]. Note that during the simulation run, the instantaneous throughput temporarily decreases the idea load at 40 s (up to 0.33 in the example considered), but ultimately it increases and stabilizes to the saturation value. The reason why the throughput is similar to the overload condition at 40 s is that most of nodes select the same channel to transmit their packets, and after passing a longer completion period, the nodes can obtain a successful transmission opportunity after the channel has been saturated. In this work, system throughput analytical model is built in saturation throughput condition without PU communication. Otherwise, the system throughput is much less than the saturation value, as shown in Fig.6.
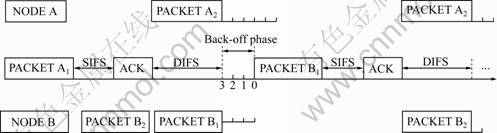
Fig.4 Packet transmission with basic access mechanism
Fig.5 Packet transmission with RTS/CTS access mechanism
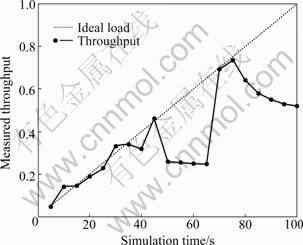
Fig.6 Unstable throughput with increasing simulation time
Table 1 Program and simulator parameters

In the throughput analytical model of the proposed protocol, we assume a fixed number of nodes, with each always having a packet available for transmission. In other words, the transmission queue of each node is assumed to be always nonempty. Firstly, we study the behavior of a single node with a tridimensional Markov model, and we obtain the general throughput formula. Then, by studying the difference among three access mechanisms, we express the throughput of Basic and RTS/CTS access mechanisms. By comparing the model results with that obtained with the NS2 simulator, the dependence of the throughput on the parameters (network size, maximum back-off stage, initial contention window size, available channel and packet size) is analyzed.
3.1 Packet transmission probability
Consider a fixed number N of communicating nodes and q of available channels (N nodes can form N/2=n communication links; N is even; n≥q). In saturation conditions, each source node has immediately a packet available for transmission, after the completion of each successful transmission. Each packet needs to wait for a random back-off time before the next transmission.
Let b(t) be the stochastic process representing the back-off time counter for a given node. A discrete and integer time scale is adopted. t and t+1 correspond to the beginning of two consecutive slot times and the back-off time counter of each node decrement at the beginning of each slot time.
Since the value of the back-off time counter of each node depends also upon its transmission history, the stochastic process b(t) is non-Markovian. However, for convenience, we define W=CWmin. Let m be the value of the maximum back-off stage, and then CWmax=2mW. Adopt the notation Wi=2iW, where i![]() [0, m], called “back-off stage.” Let s(t) be the stochastic process representing the back-off stage [0, …, m] of the node at time t. Let c(t) be the stochastic process representing the available channel [0, …, q] of the station at time t.
[0, m], called “back-off stage.” Let s(t) be the stochastic process representing the back-off stage [0, …, m] of the node at time t. Let c(t) be the stochastic process representing the available channel [0, …, q] of the station at time t.
In this model, we assume that each packet collides with constant and independent probability p, regardless of the number of retransmissions suffered. It is intuitive that this assumption is more accurate as long as W, n, q and m get larger. p is referred to as conditional collision probability, meaning that the probability of a collision is seen by two packets being transmitted on the same channel.
Once the independence is assumed and p is supposed to be a constant value, it is possible to model the tridimensional process {s(t), b(t), c(t)} with the discrete time Markov chain depicted in Fig.7. In this Markov chain, the one-step transition probabilities are
 (2)
(2)
The first equation in Eq.(2) accounts for the fact that, at the beginning of each slot time, the back-off time counter is decremented. The second equation accounts for the fact that a new packet following a successful packet transmission starts with back-off stage 0, and thus the value of the back-off time counter is initially uniformly chosen in the range of [0, W0-1]. Other cases model the system after an unsuccessful transmission. As considered in the third equation of Eq.(2), when an unsuccessful transmission occurs at back-off stage of i-1, the back-off stage increases, and the new initial back-off time counter value is uniformly chosen in the range of [0, Wi-1]. The fourth equation in Eq.(2) accounts for the fact that the node switches the next available channel to compete the transmission opportunity, after an unsuccessful transmission and the back-off stage reach the maximal value m. Finally, the fifth case models the fact that once the back-off stage reaches the value m and it is the last available channel, the back-off stage is not increased in the subsequent packet transmissions.
Let![]() i
i![]() [0,
[0,
m], k![]() [0, Wi-1], l
[0, Wi-1], l![]() [0, q] be the stationary distribution of the chain. We now show that it is easy to obtain a closed form solution for this Markov chain. First, note that
[0, q] be the stationary distribution of the chain. We now show that it is easy to obtain a closed form solution for this Markov chain. First, note that

 (3)
(3)

Fig.7 Tridimensional discrete time Markov chain model
Owing to the three equations in Eq.(3), all the values of bi,k,l are expressed as functions of the value b0,0,0 and of the conditional collision probability p. b0,0,0 is finally determined by imposing the normalization condition, which is simplified as
![]() (4)
(4)
from which
![]()
![]() (5)
(5)
We can now express the probability τ that a node transmits in a randomly chosen slot time. As any transmission occurs when the back-off time counter is equal to zero, regardless of the back-off stage and channel, it is
![]()
![]()
![]() (6)
(6)
As a side note, it is interesting to highlight that, when m=0 and q=0 (no exponential back-off stage and multichannel are considered), the probability τ becomes to be independent of p, and Eq.(6) becomes the much simpler one independently found in Eq.(7) for the constant contention window problem:
![]() (7)
(7)
In general, τ depends on the conditional collision probability p. To find the value of τ, we note that the probability p that a transmitted packet encounters a collision is the probability that, in the same time slot and channel, at least one of the (n-1) transmits remaining source nodes. At the steady state, each remaining source node transmits a packet with probability τ. This yields
p=1-(1-τ)n-τ(1-τ)n-1 (8)
In order to express the probability p, the equation is divided into three parts. The second term accounts for the probability of all the nodes waiting for transmitting packets. The third term expresses that only one node can transmit a packet and others cannot. Through the foregoing analysis, there is no need to consider the parameter q in Eq.(8), and then, it becomes the much simpler equation found in Eq.(9):
p=1-(1-τ)n-1 (9)
Equations (6) and (9) represent a nonlinear system in the two unknown variables τ and p, which can be solved using numerical techniques. It is easy to prove that this system has a solution. In fact, inverting Eq.(9), we obtain
![]() (10)
(10)
This is a continuous and monotone increasing function in the range p![]() (0, 1), which starts from τ*(0)=0 and grows up to τ*(1)=1. Equation (6) is also continuous in the range p
(0, 1), which starts from τ*(0)=0 and grows up to τ*(1)=1. Equation (6) is also continuous in the range p![]() (0, 1). Moreover, τ(0)=2/(W+1), τ(1)= 2/(1+2mW). One of the solution is now proven noting that τ(0)>τ* and τ(1)>τ*(1).
(0, 1). Moreover, τ(0)=2/(W+1), τ(1)= 2/(1+2mW). One of the solution is now proven noting that τ(0)>τ* and τ(1)>τ*(1).
3.2 Multichannel saturation throughput
Let S be the normalized multichannel system throughput, defined as the successful transmission packet bits time taking up the total time in a slot time. To compute S, let us analyze what can happen in a randomly chosen channel and slot time. Let Ptr be the probability that there is at least one node transmission in the considered slot time. Since n source nodes contend on the channel, and each transmits with probability τ
Ptr=1-(1-τ)n (11)
the probability Ps that a transmission occurring on a channel is successful is given by the probability that exactly one source node transmits on the channel, conditioned on the fact that at least one node transmits,
![]() (12)
(12)
We are now able to express S as the ratio of
![]() (13)
(13)
where E[P] is the average packet size. The average amount of packet information successfully transmitted in a slot time is PsPtrE[P], since a successful transmission occurs in a slot time with probability PtrPs. The average length of a slot time is readily obtained considering that, with probability (1-Ptr), the slot time is empty, with probability PtrPs, it contains a successful transmission, and with probability Ptr(1-Ps) it contains a collision. Ts is the average time that the channel is sensed to be busy because of a successful transmission, and Tc is the average time that the channel is sensed to be busy by each node during a collision. σ is the duration of an empty slot time. Of course, the values E[P], Ts, Tc and σ must be expressed with the same unit.
The analytical model given above is very convenient to determine the multi-channel maximum saturation throughput when the available channel is known. Let us rearrange Eq.(13) to obtain
 (14)
(14)
As Ts, Tc, E[P] and σ are constants, the throughput S is maximized when the following quantity is maximized:
 (15)
(15)
Taking the derivative of Eq.(15) with respect to τ, and imposing it equal to 0, we obtain, after some simplifications, the following equation:
![]() (16)
(16)
Under the condition τ << 1, there is
![]() (17)
(17)
And the approximate solution is
 (18)
(18)
Equation (16) and its approximate solution Eq.(18) are allowed to explicitly compute the optimal transmission probability τ that each source node should adopt in order to achieve the maximum throughput performance within a considered network scenario. In other words, the maximum performance can be achieved for every network scenario, through a suitable sizing of the transmission probability τ in relation to the number of the source nodes and access mechanism.
However, Eqs.(6) and (9) show that τ also depends on the network size and on the system parameters m, q and W. As n is not a directly controllable variable, the only way to achieve the optimal performance is to employ adaptive techniques to tune the values m, q and W on the basis of the estimated value of n.
3.3 System performance analysis for basic and RTS/ CTS access mechanism and simulation results
The multi-channel system throughput expressed by Eq.(13) is further specifically computed, and then the parameters Ts and Tc which are unknown in the throughput expression are necessary to specify by Basic and RTS/CTS access mechanisms of the proposed protocol. The performance analysis is then obtained through the simulator and analytical model.
1) Basic access mechanism
Let us first consider a system completely managed via the basic access mechanism. Let H=TP-hdr+TM-hdr be the packet header, and δ be the propagation delay. As shown in Fig.8, in the basic access case, we obtain
![]() (19)
(19)
where E[P] is the length of packet size involved in a collision. In the ideal basic access mechanism case, only one collision may occur between two packets, as shown in Fig.8.
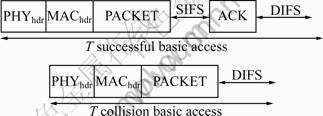
Fig.8 Basic access mechanism of collision condition
To verify the model, we have compared its results with those obtained with the modified multi-channel 802.11 DCF NS 2.29 simulator, which is an event-driven custom simulation program, written in the C++ and Otcl programming language. The simulator closely follows all the proposed multi-channel modified 802.11 protocol details for each independently transmitting node. In particular, it can emulate the real operation of each node, including the propagation times, turnaround times and the CIW information exchange. However, the model cannot exactly compute all the aspect of the protocol, unless otherwise specified, the model analytical results are only compared with the simulation results in DW, and the parameters are reported in Table 1.
Figure 9 shows that the analytical model is accurate for the basic access mechanism: analytical results practically coincide with the simulation results. All simulation results are obtained with above 95% confidence interval less than 0.001. In the simulation run, the different available channel system throughputs are compared by closing a transmission channel, as shown in Fig.7. We obtain the result that saturation throughput is highly dependent on the available channel. Figure 9 also reports that the throughput strongly depends on the number of nodes in a network. In most cases, the greater the network size is, the lower the throughput is.
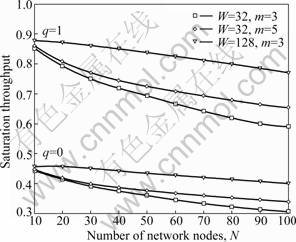
Fig.9 Multichannel saturation throughput in different network sizes for basic access mechanism
Figure 10 shows that the saturation throughput also has a high dependence on the transmission probability τ, which leads to the similar throughput value in different network sizes. The throughput computed by Eq.(16) is compared with the approximate value obtained by Eq.(18) in Table 2. Note that the saturation throughput is greater in the basic access case, as τ is greater.
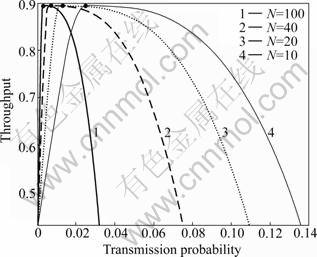
Fig.10 Multichannel saturation throughput with different transmission probabilities for basic access mechanism
Figure 11 shows the dependency of the throughput on the initial contention window size W. We have assumed the number of back-off stages equal to 5 and in four different network sizes. It is reported that the throughput of the basic access mechanism strongly depends on W, the size of network. For example, a high value of W gives excellent throughput performance in the case of 50 contending nodes, while it drastically penalizes the throughput in the case of small number of contending nodes. We find that large value of W limits the throughput of a single node, which, when alone in the channel, is bounded by
![]() (20)
(20)
where E[P] and Ts are the average packet size and the average channel holding time in case of successful transmission. Equation (20) is directly obtained from Eq.(13) by observing that, as there are no other nodes which can collide with the considered one, the probability of success Ps is equal to 1, and q is equal to 0, when only one channel used is considered. In addition, the probability Ptr that a transmission occurs on the channel is equal to the probability τ that the node transmits. As the conditional collision probability p equal to 0, Ptr=τ is given by Eq.(7).
Table 2 Comparison between maximum throughput and approximate throughput for basic access mechanism
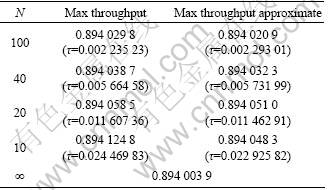

Fig.11 Multichannel saturation throughput in different sizes of back-off contention window for basic access mechanism
Figure 12 shows that the dependence of the throughput from the maximum number m of back-off stages is marginal. The figure reports the cases with W=32. We can see that the choice of m does not practically affect the system throughput, as long as m is greater than five or six.
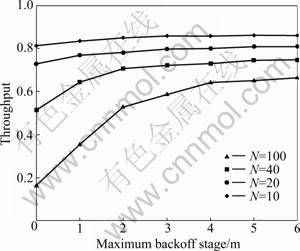
Fig.12 Multichannel saturation throughput with maximum back-off stage for basic access mechanism
2) RTS/CTS access mechanism
The RTS/CTS access mechanism is also employed in this protocol. Consider a system in which each packet is transmitted by means of the RTS/CTS access mechanism. As, in such a case, collision can occur only on RTS frames, it is (see Fig.13)
 (21)
(21)
In order to compare with the basic access mechanism, we also obtain the RTS/CTS access mechanism results from the analytical model and simulation experiments in the same parameters summarized in Table 1.
By comparing with Fig.9, a similar accuracy of the analytical model for the RTS/CTS access mechanism is shown in Fig.14. A surprising result is that the maximum throughput reachable by the RTS/CTS mechanism is very close to that achievable by the basic access mechanism. Moreover, the maximum throughput is practically independent of the number of nodes in the network. This is easily justified by noting that the throughput formula can be approximated as follows. Let K=![]() and use the approximate solution τ=1/(nK). For n sufficiently large, there is
and use the approximate solution τ=1/(nK). For n sufficiently large, there is
![]() (22)
(22)
![]() (23)
(23)
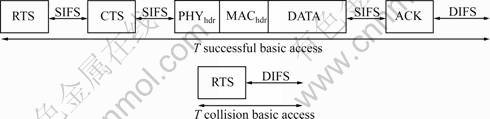
Fig.13 Ts and Tc for RTS/CTS access mechanisms

Fig.14 Multichannel saturation throughput in different network sizes for RTS/CTS access mechanism
The maximum reachable throughput can thus be approximated as
![]() (24)
(24)
which is independent of n.
An advantage of the RTS/CTS scheme is that the throughput is less sensitive to the transmission probability τ. In fact, we can see from Fig.10 and Fig.15 that a small variation in the optimal value of τ leads to a larger decrease in the throughput for the basic access case than for the RTS/CTS case. Similarly, we compare the maximum throughput with the approximate throughput in Table 3.
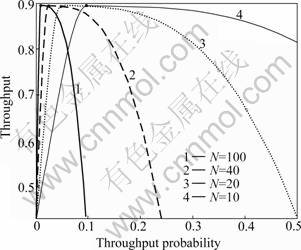
Fig.15 Multichannel saturation throughput with different transmission probabilities for RTS/CTS mechanism
Table 3 Comparison between maximum throughput and approximate throughput for RTS/CTS access mechanism

Figure 16 shows that the throughput obtained with the RTS/CTS mechanism is almost independent of the value of W, when W is less than 64. It is furthermore almost insensitive to the network size.

Fig.16 Multichannel saturation throughput in different sizes of back-off contention window for RTS access mechanism
Figure 17 shows that the dependence of the throughput from the maximum number m of back-off stages is marginal. Similar to the basic mechanism, we can see that the choice of m does not practically affect the system throughput, as long as m is greater than four or five.
3) Hybrid access mechanism
After analyzing the dependence of throughput on system parameters for the above two access mechanism, it is found that the RTS mechanism has an advantage over the basic mechanism in most of the case. It is the reason why IEEE 802.11 chooses the mechanism as the main transmission scheme. However, when the packet size is no more than the RTS frame, the performance of basic access mechanism is better than the RTS access mechanism, as shown in Fig.18. Hence, in this protocol, a hybrid access mechanism is proposed to dynamically change the transmission scheme, whose packets are transmitted by means of the RTS/CTS mechanism only if ![]() and vice verse, to maintain the high throughput.
and vice verse, to maintain the high throughput.
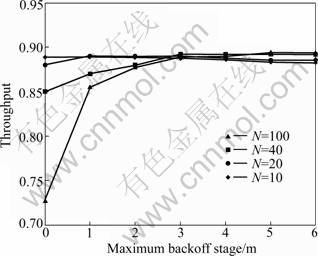
Fig.17 Multichannel saturation throughput with maximum back-off stage for RTS access mechanism
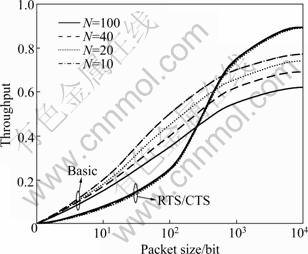
Fig.18 Throughput with increasing packet size for two access mechanisms
4) Comparison with traditional protocol
In order to verify the performance of MCRMAC protocol with modified multichannel IEEE 802.11 DCF, we have compared its results with those obtained with the original single channel IEEE 802.11 DCF by NS 2.29 simulator. The parameters are reported in Table 1. As shown in Fig.19, q=0 stands for the throughput of IEEE 802.11 single channel and the other two stand for the performance of the MCRMAC proposed in this work. So, we can see that the MCRMAC algorithm can improve the system saturation throughput with increasing communication channels. The characteristic is suitable for the cognitive radio network, and the cognitive radio node can use multi-channel to transmit multimedia data and avoid interfering in the primary users.
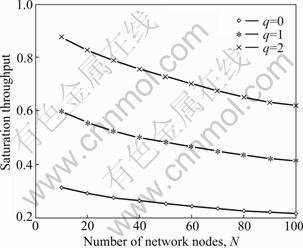
Fig.19 Saturation throughput with different communication channels
4 Conclusions
1) A distributed multi-channel MAC protocol for CR networks without common control channel is proposed. Contrary to the IEEE 802.11 working group centrally controlled MAC protocol, it is assumed that all nodes exchange information in a dynamic channel determined by the PU, source and destination nodes.
2) The protocol is based on the timing structure and multi-channel technology which is shown to effectively protect the PUs from interference, and obviously improve the performance by using spectral opportunities in licensed channels.
3) A tridimensional Markov analytical model is presented to quantitatively analyze the multi-channel system throughput based on the scheme proposed in protocol data window.
4) The comparison with simulation results shows that the model is extremely accurate in predicting the system throughput. The model shows that the performance of the basic access mechanism strongly depends on the system parameters. Conversely, the performance is only marginally dependent on the system parameters which are except for the packet size, when the RTS/CTS mechanism is considered.
5) The hybrid access mechanism is proposed to dynamically adopt access mechanism by judging the value of the throughput computed by ![]() and
and ![]() in real time.
in real time.
6) Compared with the traditional IEEE 802.11 protocol, the MCRMAC can improve the system throughput with increasing the available channel flexibly. We believe that this MAC protocol with hybrid access mechanism should be used in the majority of the practical cases.
References
[1] STEVENSON C, CHOUINARD G, LEI Zhong-ding, HU Wen-dong, SHELLHARMMER S, CALDWELL W. IEEE 802.22: The first cognitive radio wireless regional area network standard [J]. Communications Magazine, IEEE, 2009, 47(1): 130-138.
[2] HU Wen-dong, WILLKOMM D, ABUSUBAIH M, GROSS J. Cognitive radios for dynamic spectrum access: Dynamic frequency hopping communities for efficient IEEE 802.22 operation [J]. Communications Magazine, IEEE, 2007, 45(5): 80-87.
[3] HUANG Rong-sheng, FANG Yu-guang. Utilizing multi-hop neighbor information in spectrum allocation for wireless networks [J]. Wireless Communications, IEEE Transactions on, 2009, 8(8): 4360-4367.
[4] HOU Y T, SHI Yi, SHERALI H D. Spectrum sharing for multi-hop networking with cognitive radios [J]. Selected Areas in Communications, IEEE Journal on, 2008, 26(1): 146-155.
[5] WANG Jian-xin, MAKFILE S, LI Jing. A random adaptive method to adjust MAC parameters in IEEE802.11e WLAN [J]. Journal of Central South University of Technology, 2006, 13(4): 629-634.
[6] WINTER R, SCHILLER J, NIKAEIN N, BONNET C. Crosstalk: Cross-layer decision support based on global knowledge [J]. Communications Magazine, IEEE, 2006, 44(1): 93-99.
[7] SU Hang, ZHANG Xi. Cross-layer based opportunistic MAC protocols for QoS provisionings over cognitive radio wireless networks [J]. Selected Areas in Communications, IEEE Journal on, 2008, 26(1): 118-129.
[8] CHEN Wen-Tsuen, LIU Jen-Chu, HUANG Ting-Kai, CHANG Yu-Chu. TAMMAC: An adaptive multi-channel MAC protocol for MANETs [J]. Wireless Communications, IEEE Transactions on, 2008, 7(11): 4541-4545.
[9] TIMMERS M, POLLIN S, DEJONGHE A, VAN DER P L, CATTHOOR F. A distributed multichannel MAC protocol for multihop cognitive radio networks [J]. Vehicular Technology, IEEE Transactions on, 2010, 59(1): 446-459.
[10] BANY S H, KRUNZ M. Channel access protocols for multihop opportunistic networks: Challenges and recent developments [J]. Network, IEEE, 2009, 23(4): 14-19.
[11] RAJASEKARAN S, SHARMA D, AMMAR R LOWNES N, LOWNES N. An efficient randomized routing protocol for single-hop radio networks [C]// International Conference on Parallel Processing: ICPP, 2010: 160-167.
[12] ABOUEI J, BAYESTEH A, KHANDANI A K. Delay-throughput analysis in decentralized single-hop wireless networks [C]// International Symposium on Information Theory: ISIT, 2007: 1401-1405.
[13] VU M, TAROKH V. Scaling laws of single-hop cognitive networks [J]. Wireless Communications, IEEE Transactions on, 2009, 8(8): 4089-4097.
[14] DEJONGHE A, BOUGARD B, POLLIN S, CRANINCKX J, BOURDOUX A, VEN der P L, CATTHOOR F. Green reconfigurable radio systems [J]. Signal Processing Magazine, IEEE, 2007, 24(3): 90-101.
[15] CAO Li-li, ZHENG Hai-tao. Distributed rule-regulated spectrum sharing [J]. Selected Areas in Communications, IEEE Journal on, 2008, 26(1): 130-145.
[16] ZHANG Wei, MALLIK R, LETAIEF K. Optimization of cooperative spectrum sensing with energy detection in cognitive radio networks [J]. Wireless Communications, IEEE Transactions on, 2009, 8(12): 5761-5766.
[17] FENG Gui-zhu, CHEN Wei, CAO Zhi-gang. A joint PHY-MAC spectrum sensing algorithm exploiting sequential detection [J]. Signal Processing Letters, IEEE, 2010, 17(8): 703-706.
[18] PAWELCZAK P, POLLIN S, SO H S, BAHAI A, PRASAD R V, HEKMAT R. Performance analysis of multichannel medium access control algorithms for opportunistic spectrum access [J]. Vehicular Technology, IEEE Transactions on, 2008, 58(6): 3014-3031.
[19] LIAO W H, SHIH K P, CHUNG W C. Multi-channel medium access control protocol with channel distribution for mobile ad hoc networks [J]. Communications, IET, 2009, 3(12): 1821-1831.
[20] TAN Xue-zhi, XU Gui-sen, LIU Yu-tao, LIU Chun-hong. Throughput analysis of multi-channel cognitive users [J]. Journal of Harbin Institute of Technology, 2010, 42(5): 732-735. (in chinese)
(Edited by YANG Bing)
Foundation item: Project(61071104) supported by the National Natural Science Foundation of China
Received date: 2010-09-09; Accepted date: 2011-01-06
Corresponding author: XU Gui-sen, PhD; Tel: +86-15004658216; E-mail: xuguisen@hitcrc.hit.edu.cn

